In early April 2026, Proton published a comparison chart of messaging apps on social media—and unexpectedly set off a public row. Pavel Durov spotted errors in it, WhatsApp joined the argument, and Elon Musk seized the moment to promote his own app. The substantive question—which messenger is actually more secure—was left without a clear answer.
On April 10, the official Proton Pass account posted an infographic rating eight messengers against several privacy criteria. Proton’s original article had been published back in 2021 and was updated as the market changed—the latest revision came out in March 2026. In it, Telegram was described as “a popular but problematic choice.”
Durov replied in the comments: according to him, the chart contained at least several factual inaccuracies—notably on whether Telegram uses its own servers, whether end-to-end encryption is supported in group video calls, and whether registration without a phone number is possible. Proton acknowledged that the infographic did not reflect Telegram’s current state, but added that the article itself correctly states that the company is headquartered in the UAE—a country whose government is not known for high standards of privacy protection.
Asked why end-to-end encryption in Telegram is not enabled by default, Durov said it is impossible to optimize for convenience and security at the same time—it inevitably leads to trade-offs. That is why, he argued, Telegram has two modes: regular chats and secret chats. Durov’s argument was immediately turned against him: critics pointed out that most users do not even know secret chats exist and communicate in an unprotected mode.
WhatsApp entered the fray by saying that it provides end-to-end encryption by default across all personal and group conversations. Durov, in turn, pointed to unencrypted backups: most users do not enable encryption for them, meaning the contents of their chats may be accessible to cloud services. In the middle of the exchange, Elon Musk retweeted Durov’s post—not to support Telegram, but to announce his own messenger, XChat, whose release was scheduled for April 17.
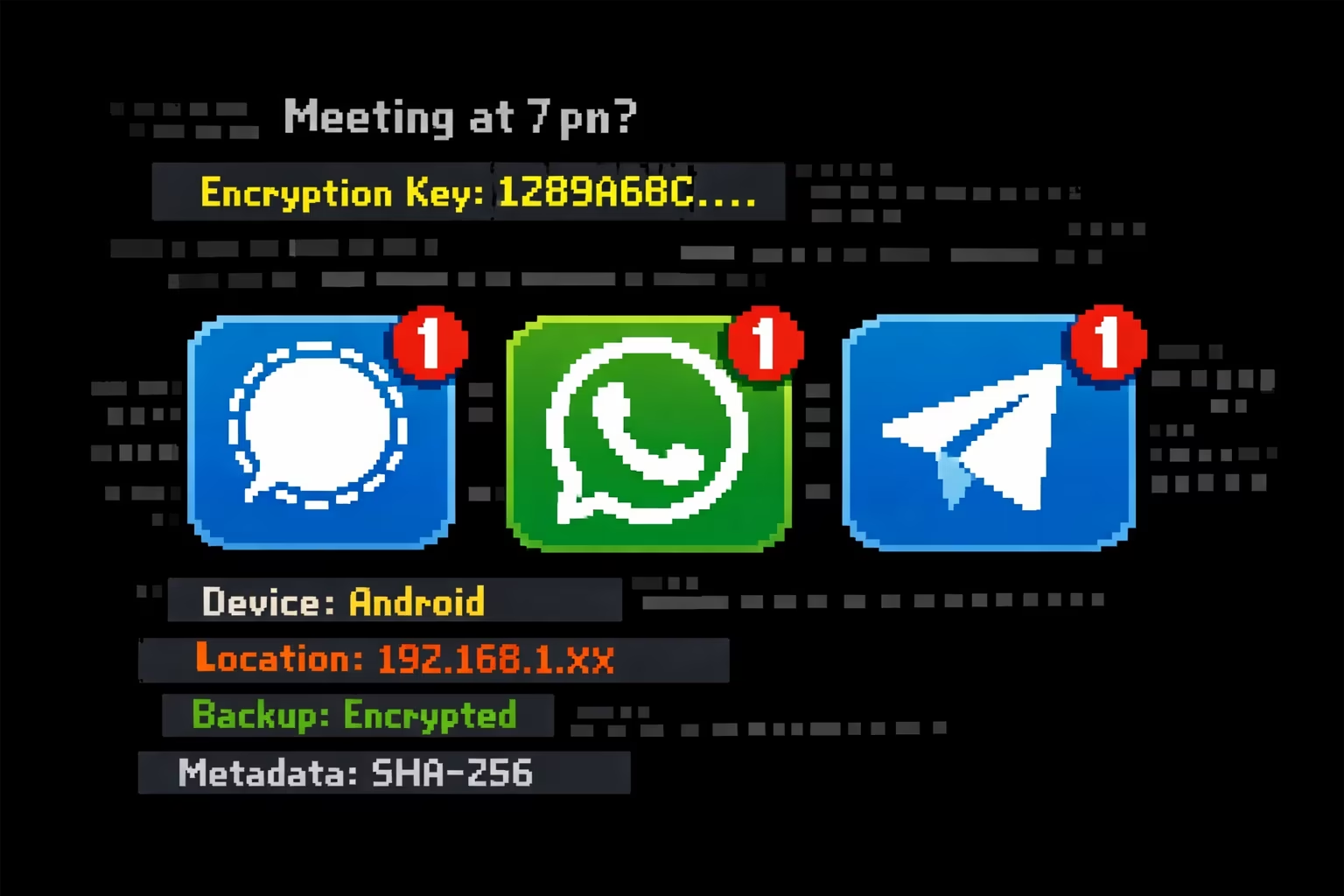
What makes the dispute notable is not only who took part in it. It exposed a broader problem: public debates about messenger security often collapse into marketing claims that are hard to verify without technical analysis. What follows is an attempt at such an analysis, based on the documented characteristics of eight apps.
What Was Compared—and How
The eight criteria cover different layers of protection—from technical architecture to the legal environment in which a company operates.
Open-source code allows independent researchers to verify the absence of hidden backdoors and vulnerabilities. Closed code requires blind trust in the developer. End-to-end encryption (E2EE) means the contents of messages are inaccessible to the company’s servers—the keys exist only for the sender and recipient. This is a basic but critically important criterion. Public audit means independent review of code and infrastructure by outside specialists. Open code without an audit does not rule out vulnerabilities.
E2EE in group video calls is technically more difficult than encrypting text messages. Many messengers solve this only partially—or not at all. Minimal metadata collection: even if the contents of a conversation are encrypted, metadata—who you talk to, when, and how often—can reveal a great deal about a person, especially when accumulated systematically. Anonymous registration without linking a phone number or email prevents identifying a user at the account level. Own servers reduce dependence on third-party cloud infrastructure subject to the jurisdiction of other countries. Jurisdiction determines which laws a company operates under and to whom it may be required to disclose data.
Comparison Table
Comparison of messaging apps by security and privacy criteria
Criterion
Signal
Telegram
Threema
Wire
Element
Olvid
Session
SimpleX
Open-source code
✓
✓1
✓
✓
✓
✓
✓
✓
End-to-end encryption
✓
✕2
✓
✓
✓
✓
✓
✓
Public audit
✓
✓3
✓
✓
✕4
✓
✓
✓
E2EE group video
✓
✓5
✓
✓
✓
✓6
✓7
✓7
Minimal metadata
✓
✕8
✓
✕
✓
✓
✓
✓
Anonymous registration
✕
✓9
✓
✕
✓
✓
✓
✓
Own servers
✕
✓
✓
?10
✓11
✕12
n/a13
n/a13
Jurisdiction
U.S.
UAE
Switzerland
U.S.14
n/a15
France
Switzerland
United Kingdom16
1 — Telegram’s server code is closed; only the client is open.
2 — E2EE works only in “secret chats.” Regular conversations, groups, and channels are encrypted only between client and server—the company can technically access them.
3 — The audit concerned the MTProto protocol, not the entire server infrastructure.
4 — At the time the table was compiled, no public audit had been conducted.
5 — Durov confirmed the presence of E2EE in Telegram group video calls in April 2026.
6 — The feature is in beta testing.
7 — Implemented with limits on the number of participants.
8 — Telegram discloses IP addresses and phone numbers as metadata at the request of authorities.
9 — Telegram allows account creation without linking a personal phone number through anonymous SIM cards or specialized services; since 2023, it has also allowed the purchase of a username without a phone number.
10 — Wire moved its legal entity to the U.S.; the question of its server infrastructure remains open.
11 — Element (the Matrix protocol) allows users to deploy their own server (self-hosting).
12 — Olvid uses its own servers for the directory, but not for message transmission.
13 — Session and SimpleX Chat are decentralized; the concept of “a company’s own servers” does not apply to them.
14 — Wire moved its legal entity from Switzerland to the U.S.
15 — Element is the Matrix protocol, which has no single corporate jurisdiction.
16 — SimpleX Chat Ltd is registered in the United Kingdom.
What Lies Behind the Numbers
Telegram—the most popular and the most ambiguous. The April clash exposed the central contradiction: hundreds of millions of users choose the messenger for convenience, without knowing—or caring much—that end-to-end encryption is not enabled by default. Durov is right that secret chats are technically robust. But he also acknowledges that he made a deliberate choice in favor of convenience—which means the bulk of conversations on Telegram’s servers are potentially vulnerable. There is an additional question over the UAE jurisdiction where the company is now registered: local law is not regarded as a model for protecting digital rights.
Signal—the gold standard, with caveats. On the full set of criteria, Signal remains the benchmark: E2EE by default, open and audited code, minimal metadata collection. The weakness Durov used in his argument—the episode in which the FBI extracted messages from the iPhone push-notification database—is not really a Signal problem as such: it is a limitation of Apple’s iOS operating system, not of the app’s cryptography. Even so, two real drawbacks remain: mandatory phone-number registration and U.S. jurisdiction.
Threema—costly, but consistent. The only paid messenger on the list (about $5 as a one-time purchase) has deliberately rejected the advertising model of monetization. Registration without a phone number, Swiss jurisdiction, own servers, independent audits. Its main limitation is a relatively small user base: a secure messenger is useful only to the extent that the circle of people using it is wide enough.
Session and SimpleX Chat—maximum anonymity, with niche appeal attached. Neither app requires any identification and both run on decentralized infrastructure. Session uses an architecture akin to onion routing. SimpleX Chat does not assign the user any identifier at all—connections are established through one-time keys. The price is a less intuitive interface and a far smaller reach.
Wire—degraded. Originally positioned as a secure messenger for business, Wire moved its legal entity from Switzerland to the U.S. and stores contact metadata in plain form. Registration requires an email address. For those who care about privacy, it is no longer the best choice.
WhatsApp—a separate case. The messenger was not included in Proton’s original table, but it ended up at the center of the dispute. Formally, E2EE in WhatsApp is enabled by default—and that is an important advantage over Telegram. Its weak point is backups: most users do not enable encryption for them, meaning the contents of chats end up on Apple iCloud or Google Drive servers in unprotected form. On top of that, WhatsApp belongs to Meta, which is itself a risk factor for anyone concerned about corporate surveillance.
What Suits Whom
Everyday communication
Signal
The best balance of protection and convenience. Suitable for most users willing to provide a phone number.
Anonymity—as the priority
Session / SimpleX Chat
No link to a phone number or email, decentralized infrastructure. For those who do not want to leave traces.
Corporate environment
Element (Matrix)
The ability to deploy one’s own server makes it attractive for organizations that care about control over infrastructure.
High-threat environment
Threema / Olvid
European jurisdiction, anonymous registration, independent audits. For journalists, lawyers, and activists operating in risk zones.